This article shows you how to connect to Azure using client credentials. Use this if you have chosen to use client credentials when connecting Azure, or if you're using Azure in China (a service operated by 21 Vianet).
To configure the integration, you must have Azure AD administrative access in order to create and configure a new App Registration.
- Create credentials in Azure.
- Connect 1Password SaaS Manager to your Azure tenant using these credentials.
Register the app
- Login to https://portal.azure.com/ for Microsoft Entra ID, or https://portal.azure.cn/ for Azure in China.
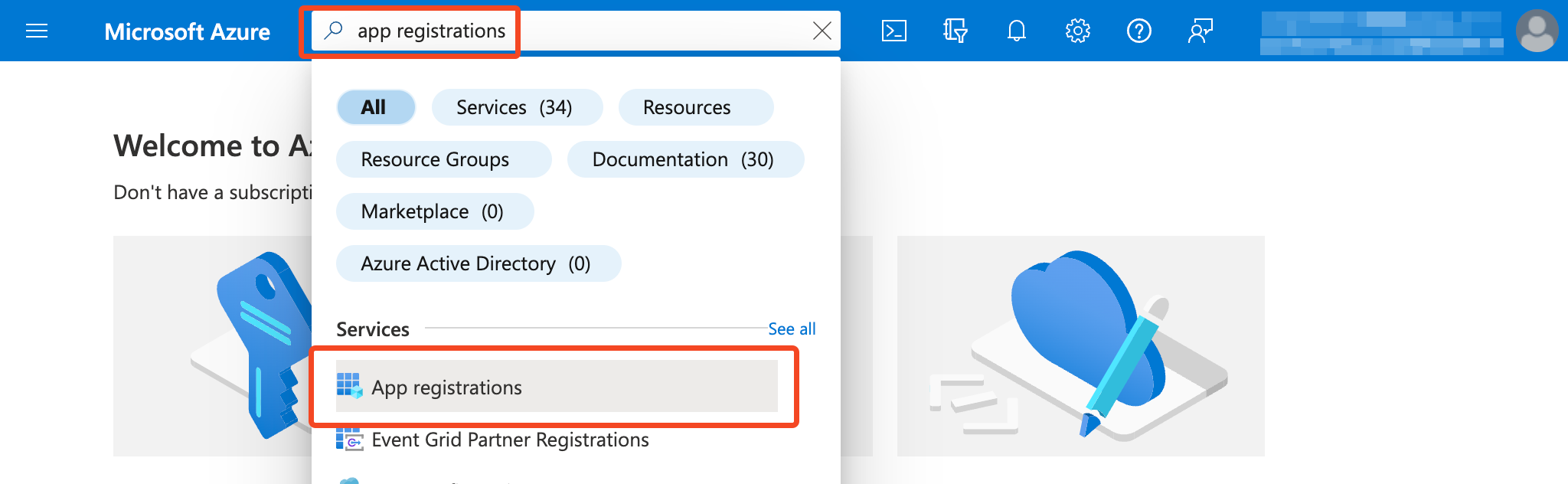
- Find App registrations:
- Select New registration.
- Enter a name, such as "SaaS Manager".
- Select Accounts in this organizational directory only (Single tenant).
- Select Register to continue. You do not need to enter a Redirect URI.
Configuring API permissions
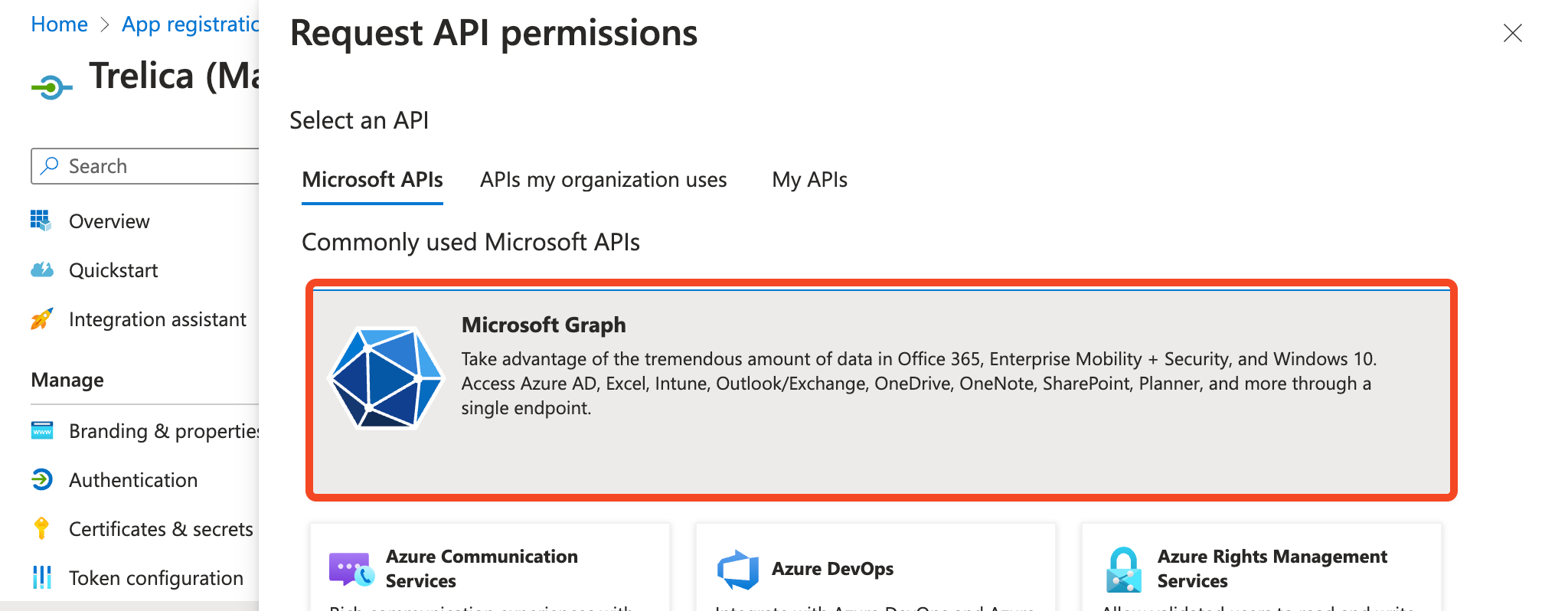
- On the API permissions tab, select Add a permission.

- Under the Microsoft APIs tab, select Microsoft Graph.
-
Select Application permissions search for each of the scopes in the table below, then select permissions depending on the features you require.
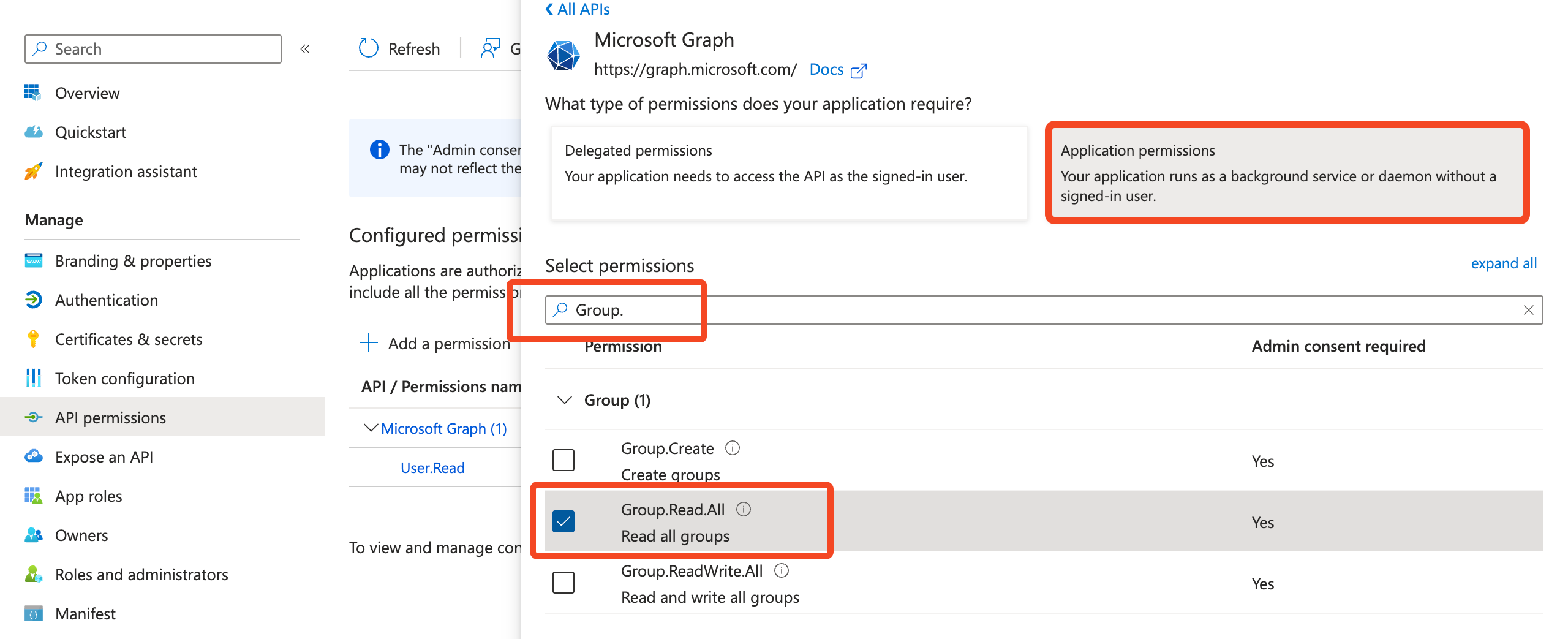
Core scopes Application.Read.AllRead applications and service principals. RoleManagement.Read.DirectoryRead directory role templates, directory roles, and memberships. Synchronization.Read.AllRead all Azure AD SCIM synchronization data. Used to understand if Azure is configured to provision and deprovision users for apps. Group.Read.AllRead groups. GroupMember.Read.AllRead the memberships of groups. Directory.Read.AllRequired to read OAuth token permissions. The integration will work without this, but won't return data about OAuth logins. User.Read.AllRead the full set of profile properties, including managers of users in your organization. AuditLog.Read.AllRead all audit log data. DeviceManagementManagedDevices.Read.AllRead the properties of devices managed by Microsoft Intune. Reports.Read.AllRead Microsoft365 usage reports. LicenseAssignment.Read.AllRead license assignments for all users. AppRoleAssignment.ReadWrite.AllAllows the app to manage user and app role assignments. ReadWrite is the minimum scope required, although SaaS Manager does not write app role assignments. IdentityProvider.Read.AllRead all identity providers. Used to return verified domains. Organization.Read.AllRead the organization and related resources. Used to return the tenant ID and name. Deprovisioning User.ReadWrite.AllUpdate the profile of every user in the organization GroupMember.ReadWrite.AllRead and write group memberships UserAuthenticationMethod.ReadWrite.AllRead and write users' authentication methods Provisioning (additional to Deprovisioning scopes) RoleManagement.ReadWrite.DirectoryRead and write directory RBAC settings -
Optionally, configure Office365 Exchange Online API Mailbox features with the integration. To do this, you'll need permissions to allow the Exchange API to make requests as an application. From the Office365 Exchange Online API, add
Exchange.ManageAsApp.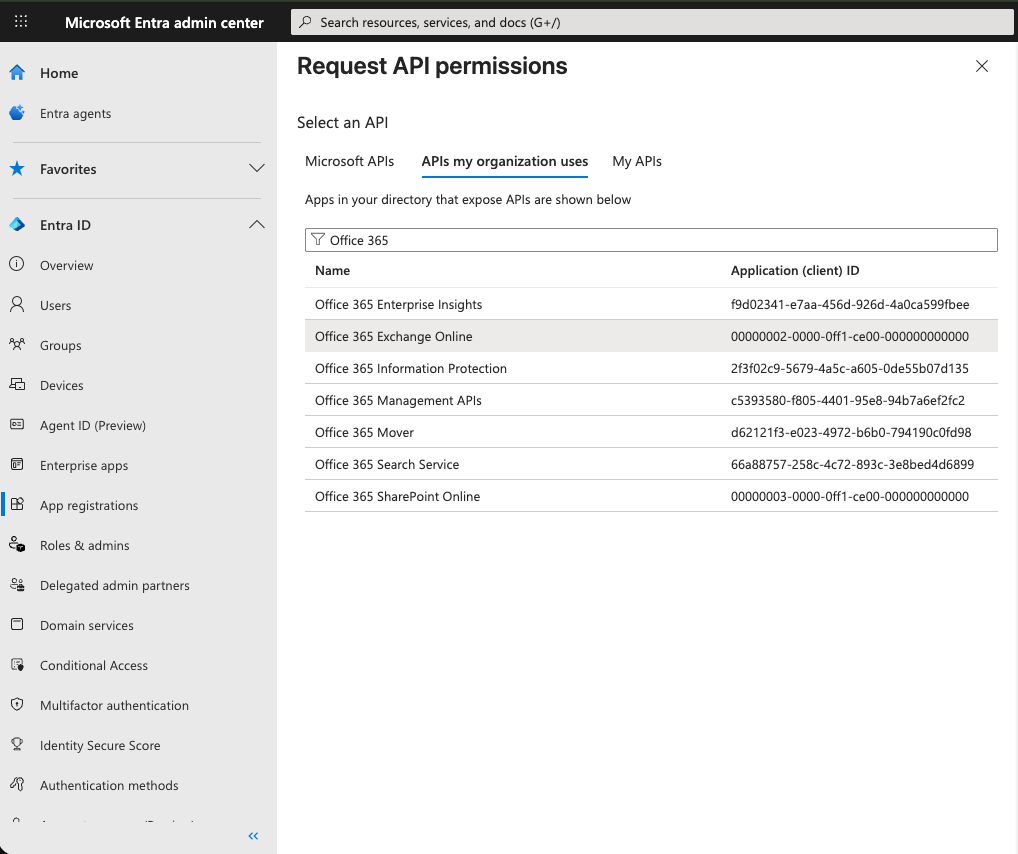
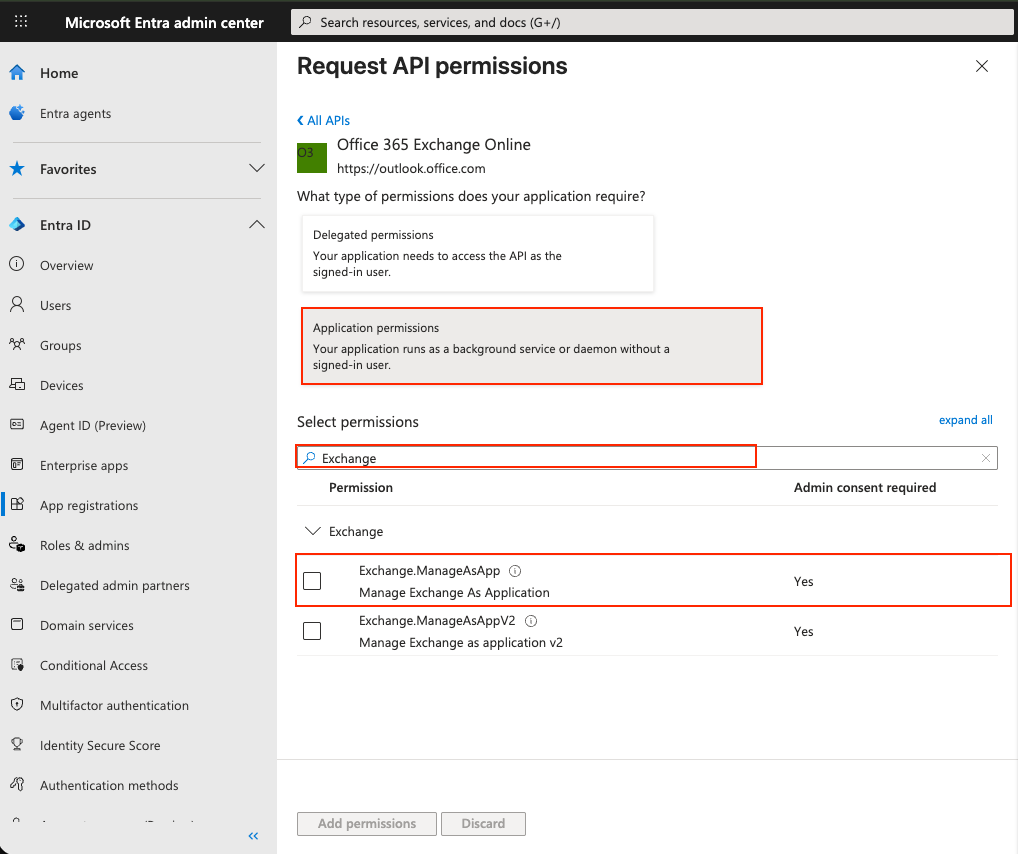
- An additional role for the Exchange API is also required if it has not already been added for the connected account. Make sure the
Exchange.ManageAsApprole is added.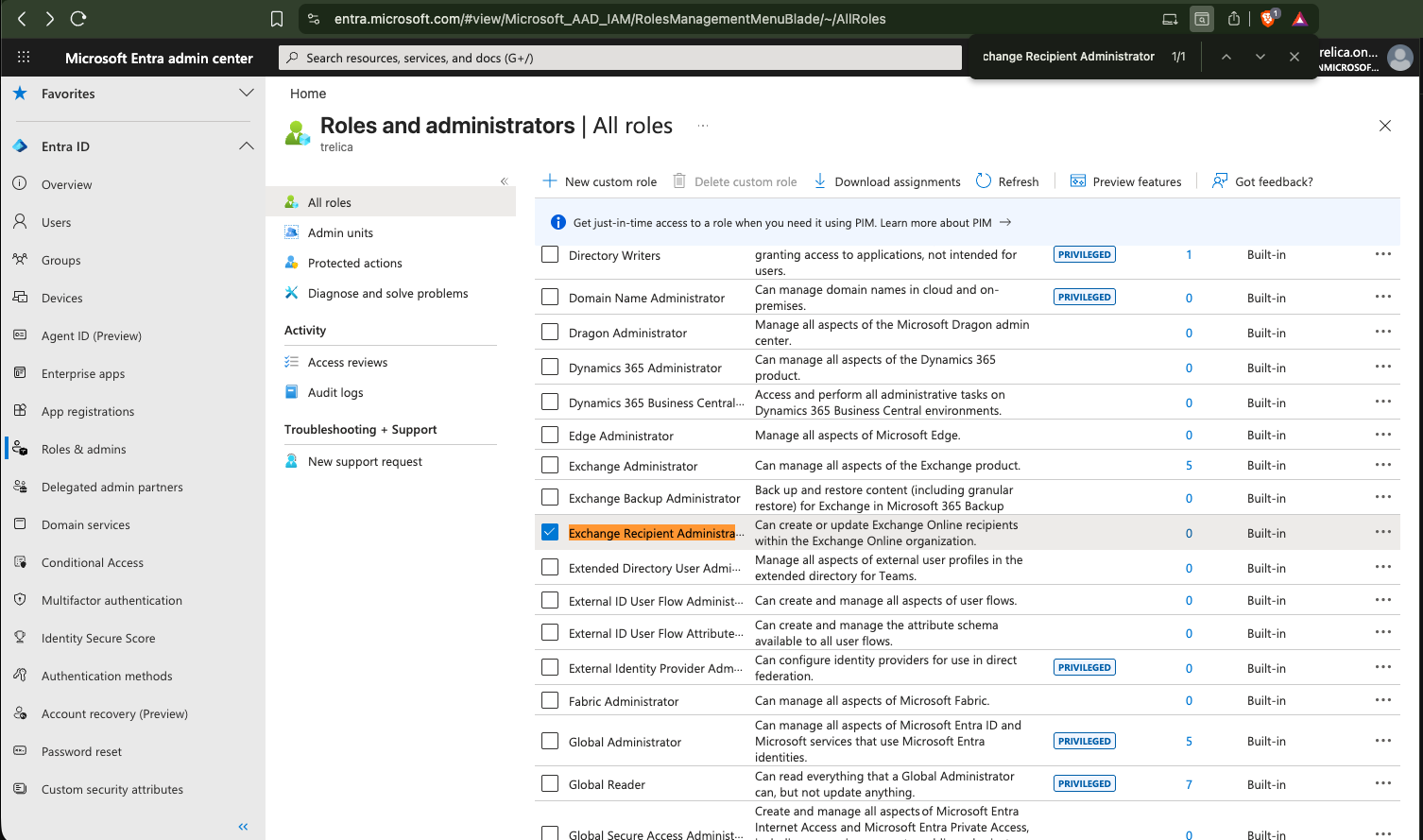
- Select Add permissions.
- Select Grant admin consent.

Create a new secret
- Go to Certificates & secrets.
- Select New client secret.
- Give the secret a name, such as "SaaS Manager", then select the expiration duration. We recommend 12 or 24 months.
- Select Add.
Collecting the IDs you need
You need three IDs which you can copy from Azure.cn:
-
From the Certificates & secrets tab, copy the Client Secret Value.
The Client Secret Value will only be available for you to copy for a short period of time. If you're unable to view or copy it, create new one.
- From the Overview tab, copy the Application (client ID) and the Directory (tenant) ID.
Connect from SaaS Manager
- In SaaS Manager, go to Integrations and choose either Azure in China or Microsoft Entra ID.
- Select Connect and enter the IDs that you gathered earlier.
- Select Connect again.
- The integration will run in the background.
Comments
0 comments
Please sign in to leave a comment.